Security’s Crucial Role in Financial Services
What comes to mind when we consider the IT systems governing financial services? Depending on the system in question, different factors take precedence. For some, availability is key; an unavailable system could directly translate to financial loss. Data consistency and integrity are paramount in others, such as banking systems. And what about confidentiality? That is crucial in nearly every case.
Can we find a single word to encapsulate all these aspects? That word is security. Security encompasses the trio of Confidentiality, Integrity, and Availability, often referred to as the cybersecurity or CIA triad. Hackers or malicious actors frequently target one or more of these dimensions, attempting to undermine a system, manipulate data according to their needs, or expose sensitive information. In the world of cybersecurity, the CIA triad is fundamental.
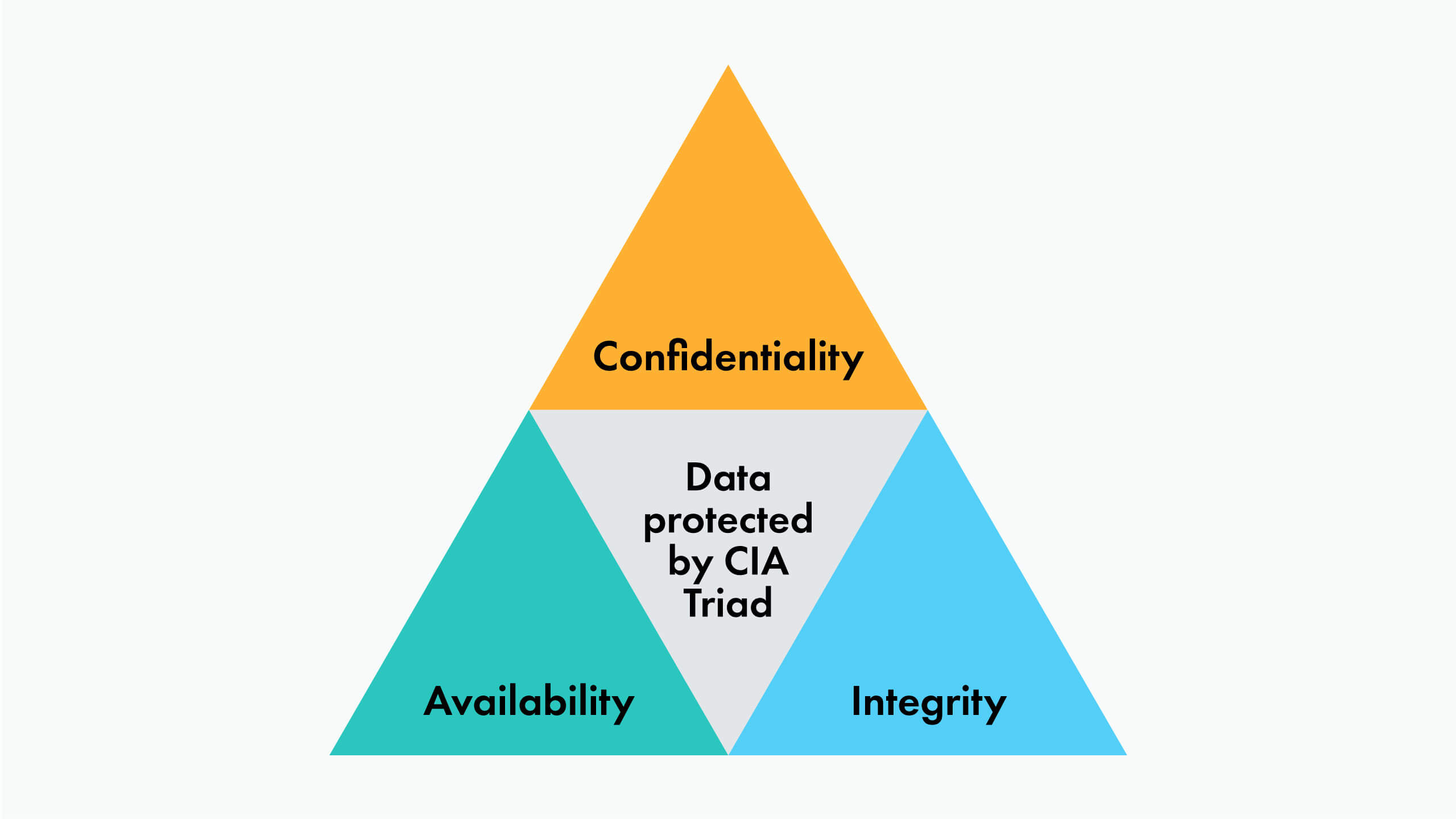
Given the centrality of the CIA triad in financial services, security naturally holds the top spot in importance.
Security, AWS Cloud, and Financial Services
For Enterprises
Enterprises usually maintain an InfoSec department tasked with implementing intrusion detection and prevention mechanisms, training employees, establishing policies, guidelines, runbooks, and more, all aimed at shielding the organization from attacks and incidents. As companies grow, so does the associated bureaucracy machinery involved in security implementation. Unfortunately, this expansion often leads to less flexibility and slower reactions to change. This dynamic proves particularly problematic when large enterprises transition from traditional colocation setups to the likes of AWS or other cloud providers.
The shift to the cloud introduces new concepts, tools, and security approaches. The InfoSec department must swiftly adapt, learning cloud-oriented security practices, altering existing rules and policies, and embracing new cloud resources. More often than not, enterprises often find themselves unprepared for this transition, inadvertently leaving numerous security vulnerabilities during the migration process.
For Startups
When it comes to startups in the financial services domain, speed is often the heartbeat. They are usually focused on launching a product as quickly as possible to generate revenue or attract investors. Leveraging cloud platforms like AWS becomes a natural choice due to its minimal capital outlays. However, the downside to this rapid pace is that things not directly related to product features often get pushed aside. And security is a frequent casualty of this approach. While startups gain traction, attracting money and users, the lack of security can lead to significant vulnerabilities, jeopardizing the company's reputation. And especially in the early stages, reputation is paramount.
Moreover, both startups and established enterprises may handle data that necessitates compliance with specific security frameworks (like PCI DSS, for instance). Identifying and bridging security gaps to prepare for audit requirements can be time-consuming.
The Emergence of AWS Security Hub
In my professional journey, the AWS Security Hub has proven to be an invaluable asset in the projects where we have implemented it. Used in conjunction with AWS GuardDuty, AWS Inspector, and AWS Firewall Manager, it facilitates the establishment of a robust security posture, all achieved with minimal effort and cost. Here are some key features of Security Hub that make it particularly beneficial for financial services:
- Ongoing Security Checks: Security Hub provides continuous checks for best practices and compliance tailored to AWS. It currently supports controls for standards such as:
- AWS Foundational Security Best Practices (FSBP) standard
- Center for Internet Security (CIS) AWS Foundations Benchmark v1.2.0 and v1.4.0
- National Institute of Standards and Technology (NIST) SP 800-53 Rev. 5
- Payment Card Industry Data Security Standard (PCI DSS)
The activation of these security checks requires just a few clicks. Explicitly designed for AWS, this feature can swiftly evaluate AWS services configuration, making it one of the quickest ways to assess infrastructure security.
- Aggregation of Findings: Large enterprises or product companies commonly operate across multiple AWS accounts, leading to challenges in centralizing data collected from various security products into a single dashboard. This process involves multiple IAM users (1 per integration per account) or centralized log storage, both of which can introduce extra costs and require additional efforts to establish baselines for new accounts. Security Hub simplifies this process by aggregating organizational findings into a single interface, all with just a few clicks. We found this feature exceptionally useful.
- Prioritizing Findings: Security Hub is equipped with the ability to estimate the issues’ severity, aiding in prioritization. This is particularly beneficial when the security or cloud team may not have a deep understanding of the cloud environment, ensuring effective issue prioritization.
Integration with AWS Services and External Sources
AWS Security Hub (SH) supports integration with a plethora of AWS services such as Config, Firewall Manager, Guard Duty, Inspector, and many others, including a substantial number of third-party security analysis and monitoring tools. Furthermore, it offers customizable integration options, expanding its capabilities and adding proactive activity monitoring, not only infrastructure configuration. The outcome is a unified aggregation of all security-related facets in one convenient unified platform with minimal effort.
Exporting Findings to Third-Party Tools
While not an out-of-the-box feature, the automation capabilities provided by Security Hub enable data export to third-party tools. If Security Hub is not intended to be the main security dashboard within an organization, its events and API can be used to create custom integrations with a tool of your choice, allowing the translation and aggregation of findings elsewhere. Additionally, Security Hub permits exporting findings to tools like Jira, converting them into actionable items, an incredibly valuable asset.
Capabilities for Implementing Auto-Remediation
Security Hub’s automation rules and integration with EventBridge, allow the engineering team to react to findings and trigger automation to implement auto-remediation. This approach has enormous potential for continuous security improvement and automatic, instantaneous incident response.
Alerting and Integration with Incident Response Tools
The capabilities as mentioned earlier also enable integration with incident response tools and alerting, providing substantial potential for automation.
A Strategic Approach
For financial services that are either newly hosted in AWS or planning to make a move and find themselves in situations similar to those described earlier, I propose a pragmatic 4-step strategy: Enable, Monitor and React, Adjust and Integrate, and Automate.
- Enable: Do it right from the start. This low-hanging fruit is not free, with costs depending on the number of checks per month, but even in a large organization with 50+ accounts, the $100-200 USD expense is trivial.
- Monitor and React: Keep an eye on your dashboard, observe findings, schedule regular review sessions, prioritize remediation actions based on your circumstances, and implement basic alerting mechanisms.
- Adjust and Integrate: As you progress on your cloud journey, modify configurations, incorporate new integrations, and, if needed, align with the tools of your InfoSec department. Continue to adapt and tap into Security Hub's capabilities.
- Automate: As you become more comfortable in the cloud, introduce auto-remediation and incident response automation. Utilize findings to formulate preventive policies and continuously strengthen your security.
Conclusion
For financial services companies operating within AWS, Security Hub is both a foundational step towards establishing a robust security posture and a potent tool for the InfoSec department in implementing comprehensive security, monitoring, analysis, and operational management. It can be useful in all stages of cloud adoption, from the initial transition to a fully cloud-integrated organization. Equipped with readily enabled tools, extensive integration options, and automation capabilities, Security Hub assumes the potential to become a pivotal component of the security framework for financial services.