
Privacy Preference Center
More information
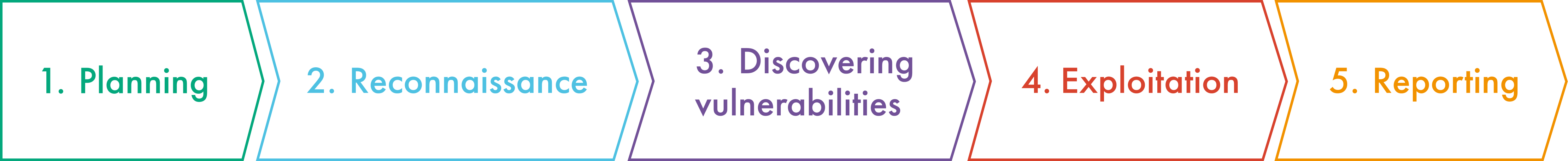
Penetration testing, commonly known as a pentest, is a controlled simulation of real-world attacks conducted by both internal and external threat actors. The primary goal is to identify vulnerabilities within an organization's security infrastructure and assess the potential impact of these weaknesses on critical business processes. By mimicking the tactics used by actual attackers, penetration testing provides valuable insights into risks, enabling organizations to strengthen their defenses against future threats.



Penetration testing as a service is a delivery platform that allows for a regular procurement of pentesting services. Thanks to PTaaS, clients can run pentests at affordable price even every single day to assure there are no code vulnerabilities.
Penetration tests and vulnerability mapping are both important when it comes to the proper security of your business. These two activities can complement each other.
Vulnerability assessment and scanning searches for security gaps within your applications/network. A thorough scan ensures any new vulnerabilities are found and patched, enabling you to focus on dealing with more serious ones quickly. However, vulnerability scans do have their limitations; they sometimes miss vital red flags and they can give false positive results.
A penetration test is more sophisticated and mimics a ‘real life’ attacker, attempting to break your system or network. Penetration testing mostly focuses on advanced cases, revealing and exploiting any types of security gaps that have not yet been discovered by the IT security staff.
It is not mandatory to have access to source code when performing a pentest. In most cases, clients can share with us some information on the organizations and their information systems. This gives DataArt security experts additional insight, so we will be able to tailor our attack vectors to testing your system’s security controls.
DataArt's penetration tests are thoroughly planned and coordinated to avoid disruption. Still, we recommend clients target a test environment or backup data to minimize potential risks and make the incident response more effective.
Penetration testing services should be used regularly, at least once a year, for regular vulnerability assessments and prevention of new attack scenarios, as well as after introducing major changes to the system.
By using our site, you acknowledge that you have read and understand our Privacy and Cookie Policy.
All trademarks listed on this website are the property of their respective owners. All rights reserved.
Copyright © 2026 DataArt
By clicking 'Accept All Cookies', you agree to the storing of cookies on your device to enhance site navigation, analyze site usage, and assist in our marketing efforts. More information

These cookies are necessary for the website to function and cannot be switched off in our systems. They are usually only set in response to actions made by you which amount to a request for services, such as setting your privacy preferences, logging in or filling in forms. You can set your browser to block or alert you about these cookies, but some parts of the site will not then work. These cookies do not store any personally identifiable information.
These cookies enable the website to provide enhanced functionality and personalisation. They may be set by us or by third party providers whose services we have added to our pages. If you do not allow these cookies then some or all of these services may not function properly.
These cookies may be set through our site by our advertising partners. They may be used by those companies to build a profile of your interests and show you relevant adverts on other sites. They do not store directly personal information, but are based on uniquely identifying your browser and internet device. If you do not allow these cookies, you will experience less targeted advertising.
These cookies allow us to count visits and traffic sources so we can measure and improve the performance of our site. They help us to know which pages are the most and least popular and see how visitors move around the site. All information these cookies collect is aggregated and therefore anonymous. If you do not allow these cookies we will not know when you have visited our site, and will not be able to monitor its performance.
All Consent Allowed